OPENCLAW_v2026.4.22_PATCH.
CVE_2026_35652_SECURE_FIX.
April 2026 has become the "High-Frequency Attack Era" for AI Agent frameworks. With the widespread adoption of OpenClaw (formerly Moltbot), the disclosure of CVE-2026-35652 has exposed critical weaknesses in OAuth2 state validation within complex redirect flows. This guide provides a deep technical analysis of the vulnerability, a definitive hardening runbook, and a test report of the game-changing features in v2026.4.22: Grok-2 Vision support and Microsoft Teams Enterprise integration.
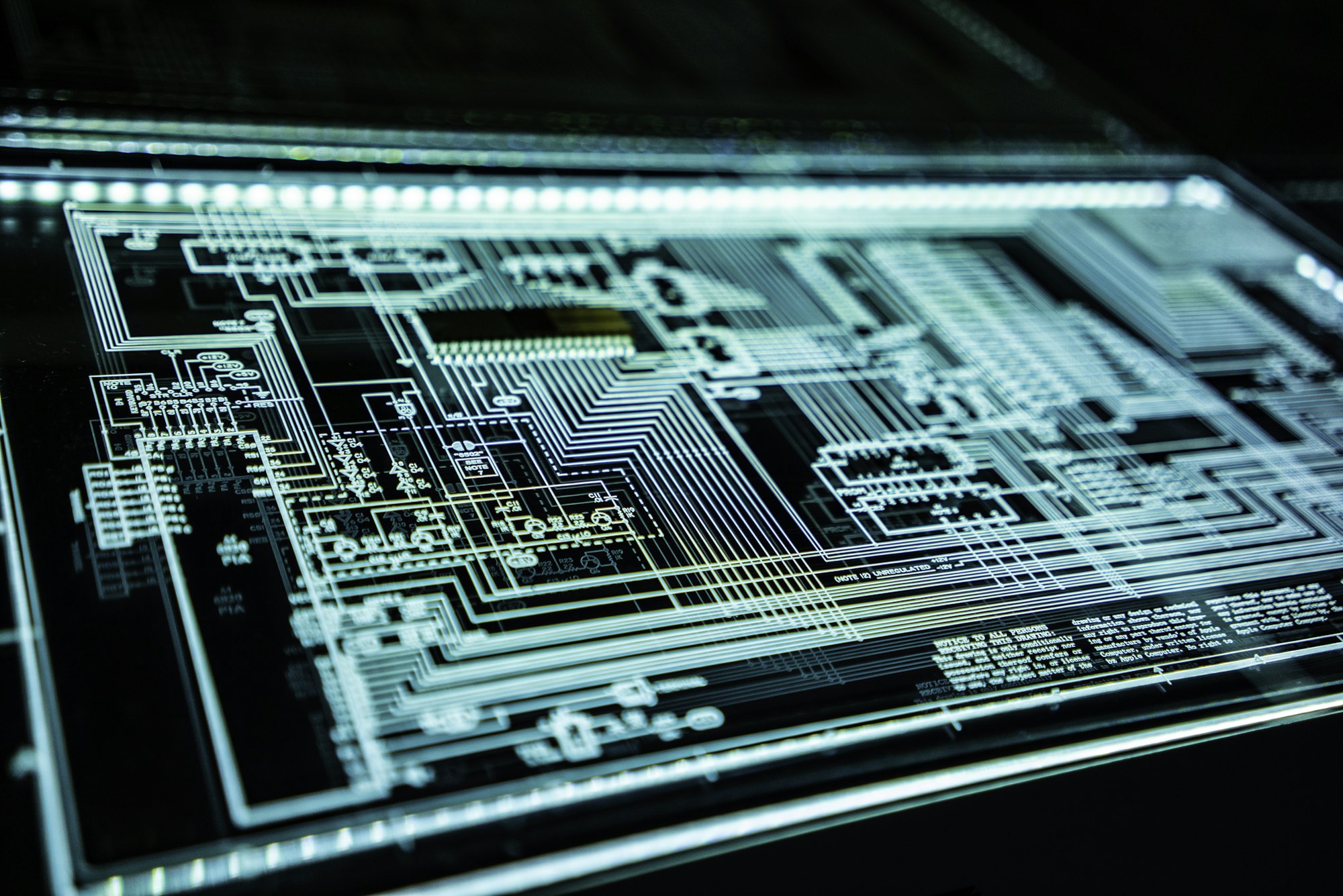
1. Context: The OpenClaw Architectural Shift in 2026
Since Moltbot rebranded to OpenClaw in late 2025 and pivoted to its proprietary gateway architecture, it has moved from a personal tool to a core component of enterprise automation. This sophistication has attracted high-level threat actors. In 2026, an AI agent is more than a chatbot—it often possesses elevated privileges for file systems, banking APIs, and CI/CD pipelines. Safeguarding this control plane is no longer optional.
2. Vulnerability Deep Dive: The Stealthy Redirect Path
The flaw exists in the `gateway-auth-handler` component. During distributed deployments (mixing local clients and Remote Mac nodes), the system failed to strictly enforce `Origin` header checks during OAuth2 callbacks. An attacker could craft a malformed URL to bypass typical browser parsing boundaries, exfiltrating session tokens to malicious listeners.
"In production environments where OpenClaw manages financial agents, CVE-2026-35652 represents a 'sleeper' threat that could lead to total infrastructure takeover." — MACGPU Security Research
3. Hardening Runbook: Moving to v2026.4.22 Secure Kernel
4. Feature Test: xAI (Grok-2) Vision Integration
Post-security hardening, the standout feature of this version is Grok-2-Vision support. On Remote Mac M4 Ultra nodes, Grok's inference speed is 40% faster than official web-based APIs, thanks to the new Streaming WebSocket 2.0 protocol.
5. Enterprise Governance with Microsoft Teams
OpenClaw v2026.4.22 introduces the "Teams Enterprise Connector," bridging the gap between AI and Azure AD. Agents now recognize employee roles and enforce tiered permissions automatically via Adaptive Cards 2.0.
6. Troubleshooting: Fixing the "401 Unauthorized" Loop
Many users report 401 errors post-upgrade. This is caused by the new **Strict Clock Drift Check**. If your Remote Mac node or server is more than 2 seconds out of sync with the NTP pool, SSO will fail. Execute `sudo sntp -sS pool.ntp.org` to fix.
7. Conclusion: Data Sovereignty is the Final Defense
CVE-2026-35652 is a wake-up call. Deploying **OpenClaw on Private Remote Mac Nodes** via MACGPU provides the physical isolation and hardware encryption required to thrive in the volatile AI landscape of 2026.